Blog
Blueborne Allows Attackers to Control Your Bluetooth-Enabled Devices
In April 2017, The Automated Reporting Management Information System (ARMIS) contacted Microsoft, Apple, Samsung, and Linux to report eight zero-day vulnerabilities related to connections via Bluetooth, designated as Blueborne.
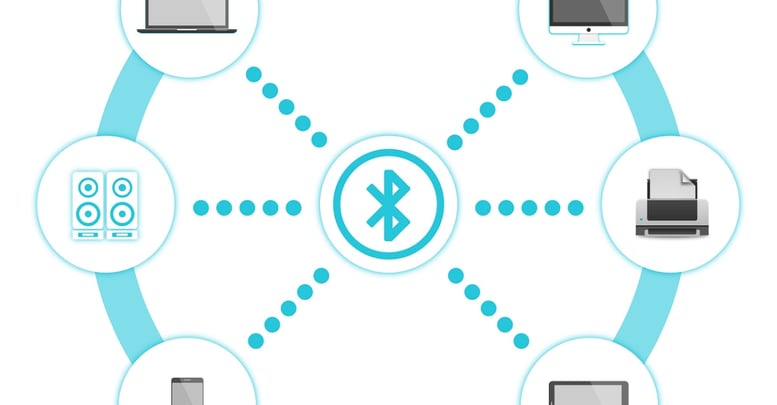
Blueborne endangers millions of unpatched devices by spreading through the air, across a wide variety of platforms: mobile, desktop, and IoT operating systems which includes Android, iOS, Windows, Linux; and all related devices that use these operating systems.
What is Blueborne?
Blueborne is a vulnerability by which attackers take advantage of Bluetooth connections to remotely control a device. The attack itself does not require the attacker's device to be paired with the target device, or require it to be in a discoverable state. It does, however, require the attacker to be within proximity of the device for the initial connection.
How does Blueborne work?
Using Man-in-the-middle attacks, the attacker will secretly intercept communication between a Bluetooth device and its intended paired device, allowing for the modification of the traffic before it arrives to one device or another.
For example, suppose Jack and Tom are trying to relay important information to each other via email and want to make sure that their communications cannot be read by third-parties.
Tom decides to setup a secure site that only Jack, and Tom can access. Jack messages Tom asking for his login credentials to the site, which is intercepted by Alex—an attacker, who then relays that message to Tom. Tom responds with the requested credentials, which are again intercepted by Alex.
Alex adjusts the credentials to go to a site he controls and sends them back to Jack. Jack uses those modified credentials unwittingly and sends a secure message to who he believes is Tom, asking for Tom to meet him at the local restaurant to drop-off an important package. Alex uses this information, and uses Jack's intended credentials to tell Tom to instead meet down by the river to drop-off the package.
Tom goes to the river, and is robbed of the package, while Jack ends up at the restaurant wondering what happened to Tom.
By spreading through the air, Blueborne takes advantage of the weakest spot in a network's defense, allowing it to spread from device to device. This makes the vulnerability incredibly infectious. As it spreads, it allows for the exploitation of high-level functions of an operating system, essentially giving an attacker full control over a device and its communications.
The attacker can then use these devices for cyber espionage, data theft, creating botnets, or to spread ransomware through a network.
How to Secure your Devices against Blueborne
ARMIS disclosed the threat to manufacturers and vendors to allow for a response of the vulnerabilities, before releasing the information to the public in September of 2017. This gave most manufacturers enough time to implement a patch to protect devices against the vulnerability.
How to Implement Released Vulnerability Patches
The best way to protect your machine against vulnerabilities is to make sure that your device is always up-to-date; running updates on your devices as soon as they become available.
- Microsoft has applied patches to all currently supported operating systems. This includes server operating systems: 2008+ and workstation operating systems: Windows 7+. Running Windows Update will patch the vulnerability.
- Apple's affected devices include iOS and Apple TV. MacOS is not affected on supported operating systems. The recommended fix is to update iOS devices to version 10 or later, replace Apple TV devices with newer tvOS devices (4th or 5th generation tvOS are not affected), and to upgrade macOS to Mountain Lion or later.
- Android implemented a patch in the September Security Rollout release. Make sure to update your phone with the latest security rollout.
- Linux has released newer kernels to address the vulnerability. In major flavors such as: Ubuntu, RedHat, CentOS, etc. this will be fixed by running the built-in updates. Other flavors of Linux may require users to navigate to the developer's website where they downloaded the operating system originally and determine what next steps are needed to patch the vulnerability.
- Other Devices such as vehicles, smart wearables, and appliances are also affected if they have Bluetooth functionality. It is recommended to go to the vendor’s website to see what response they have for patching vulnerabilities; and they will have further instructions on how to protect affected devices.
How to Protect Devices that are no Longer Supported
If you are using a device that is no longer supported by the manufacturer, the recommended fix would be to completely turn off Bluetooth when it is not being used. Users should be especially wary of using Bluetooth in public places: airports, coffee shops, parks, etc.
Replacing devices with newer, supported hardware will always be the best way to protect your personal and private information.
Other Mobile Device Recommendations
The Blueborne vulnerability is a good example of why having your devices secured is an important step to take in protecting your personal information. Some other, quick steps you can take to improve security on your devices are:
- Shut off your Bluetooth while it is not being used. While patched devices are no longer vulnerable to this attack, Bluetooth when on, is always broadcasting a signal. Other vulnerabilities could be found later putting your devices at risk. As a bonus, battery life on devices are improved when Bluetooth is off and not broadcasting
- Make sure to lock your device. Whether it be with a password, PIN, or biometrics; this will prevent thieves from accessing your personal information in the event of the device being stolen.
- Don't leave your devices unattended. Even if it is only for a couple of minutes, put your phone in your pocket or purse. Laptops should be locked with a password, and a physical locking device if being used in public.
Security can often be an inconvenience due to the added steps of accessing your devices. Your personal information is not worth those few extra seconds of using your device. Your identity, banking information, medical information can be at risk on unsecured, and unpatched devices.
Your information is worth the added time and security.
Read On
Windows Server 2016 Support Is Ending: Don’t Just Replace It. Rethink It.
Windows Server 2016 reaches the end of extended support on January 12, 2027.
Integrity Technology Solutions Recognizes Cybersecurity Awareness Month With Commitment To Online Safety And Education
Bloomington, IL — Oct. 1, 2025 — Integrity Technology Solutions is proud to announce its...
CAT Sunset: What The August 2025 Deadline Really Means For Financial Institutions
If you built your cybersecurity program around the FFIEC Cybersecurity Assessment Tool (CAT), you...


Leave a Reply